Hackers are using fake CAPTCHA verification pages to trick Windows users into running malicious Powershell commands that install the Stealth stealer software.
The campaign published SteelSee, an information-stealing tool that targets browser credentials, cryptocurrency wallets, Steam accounts, Outlook login data, system information, and screenshots. The stolen data is sent to command-and-control (C2) servers using RC4-encrypted HTTP traffic.
We have seen similar hacks before.
How does a fake captcha attack work?
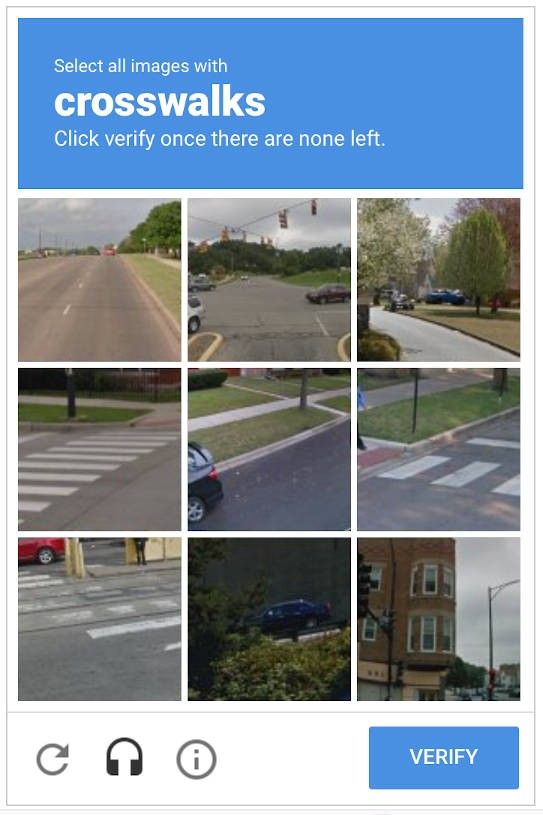
Attackers inject JavaScript into these sites. When users visit, they are redirected to a fake CAPTCHA page designed to look like the Cloudflare verification screen.
Instead of presenting a traditional image or checkbox challenge, the fake CAPTCHA instructs users to:
- Press Windows key + R
- Press Ctrl+V
- Press enter
Instructions have been prepared as part of the verification process.
This technique, called “clickfix”, takes advantage of the user’s trust in simple keyboard gestures. Victims are led to believe that they are completing routine security checks as usual.
New ClickFix attack wave is targeting Windows systems to deploy StealC Stealer
When users follow the instructions:
- A malicious Powershell command is preloaded on the clipboard.
- Pressing Ctrl + V pastes the command into the Windows Run dialog.
- Pressing Enter executes the script.
The script then connects to a remote server and downloads additional StealC Stealer malware components.
Because the command is run manually through the Run dialog, it may bypass some browser download warnings and security prompts.
Once installed, StealC starts collecting stored credentials and other sensitive data, including Outlook account details.
What clickfix with stealthy stealthy targets?
StealC specifically targets:
- browser login credentials
- cryptocurrency wallet
- steam accounts
- outlook credentials
- system information
- screenshot
This process uses encrypted HTTP traffic to talk with attacker-controlled infrastructure.
How to protect yourself from captcha scam?
A fake CAPTCHA attack depends on user interaction. The main defense is to never execute commands from web pages.
If a website asks you:
- open run dialog
- paste an order
- execute powershell
close page Immediately.
CAPTCHA challenges do not require keyboard shortcuts or system-level commands. Any such request is a big red flag.
Additional actions include:
- Avoid running PowerShell commands that you have not explicitly initiated.
- Keep Windows security features enabled.
- Monitor unusual outbound network activity if you manage enterprise systems.
- Restrict script execution and enforce application control policies in managed environments.
If you suspect you are already running such command:
- Disconnect the device from the network.
- Run a full security scan with updated security tools.
- Change passwords for Outlook, email, and other stored accounts from a clean device.
- Enable multi-factor authentication where available.
Why is CAPTCHA attack effective?
The CAPTCHA method does not rely on traditional file downloads. Instead, it uses social engineering and psychology to trick users into running malicious commands themselves.
By masquerading as CAPTCHA verification, hackers take advantage of a common and widely trusted web interaction.
The attack specifically targets Windows systems by using built-in tools such as Powershell and Run dialogs.
There is no need for a patch from Microsoft. Because it does not abuse the system vulnerability but abuses the user’s behavior.




