Xubuntu’s website was the latest website to fall victim to hackers. The attackers replaced the download link with a malicious link.
For those unaware, Xubuntu is one of the official flavors of Ubuntu, i.e. a fork/derivative of the distro. The name is a mix of Xfce and Ubuntu.
Anyway, from what I can tell user report, Attackers replaced the download links on Xubuntu.org with malicious links. So instead of downloading the .torrent file, it downloaded some zip archive which contained the malicious file.
Here’s a screenshot of what the malware looks like.

(Image courtesy) Reddit user Buty935,
Notice it says target windows version? When combined with EXE in the name, it appears that they were targeting Windows users. Perhaps users who are moving away from Windows 10, but were not familiar with Linux or torrents? Despite what users may think, it is not Linux malware. It installed itself in AppData, which only exists on Windows. The malware appears to be impersonating a GUI based downloader for Ubuntu. It runs some command prompts silently in the background to deliver the payload.
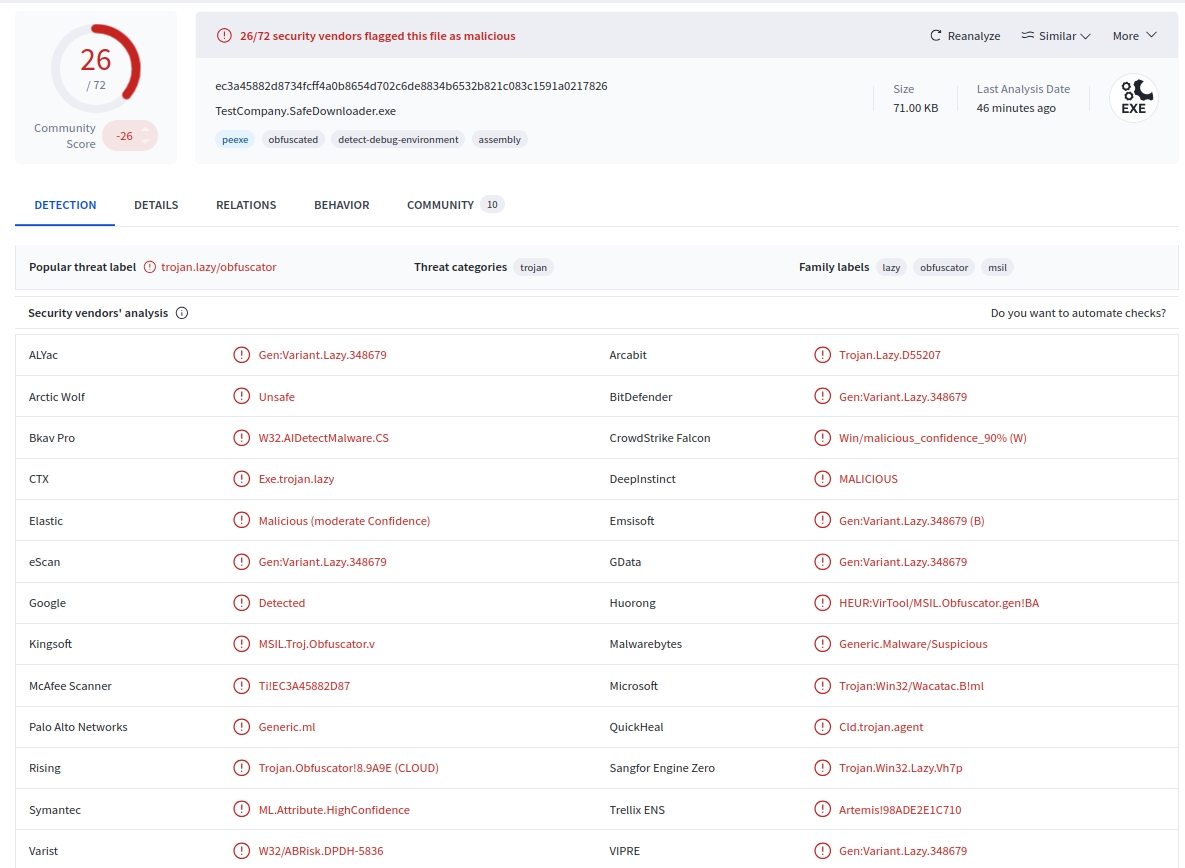
is here virustotal link For malware. The file was called “TestCompany.SafeDownloader.exe”. It has been flagged as malicious by 26/72 security vendors. Users who inspected the malware say that it is a crypto clipper. This is not a crypto miner, it is essentially a clipboard hijacking malware that targets cryptocurrencies.
According to a user hacker newsThe malware replaces the crypto wallet address in the clipboard with one belonging to the attackers.

It appears that only Xubuntu’s website was compromised, with some users saying that the torrents and releases/mirrors themselves have not been affected by the issue. Still, you should probably verify your downloads using a checksum provided by the developers.
A comment from the Xubuntu team says there was some kind of glitch with their hosting environment, and they have disabled the download page to mitigate the problem. This is a vague statement, it seems irresponsible and dismissive of the situation. How the hackers were able to compromise the servers remains a mystery. It is also not clear how many people were affected by this security lapse.
Xubuntu seems to have restored an older version of its download page, as it shows blog articles from April 2024 for Xubuntu 24.04 and 2021 instead of Xubuntu 25.10 based on Ubuntu 25.10 Questing Quokka. And the download button also doesn’t work. They’re probably in damage control mode. A post on reddit As of September 10, it has been reported that Xubuntu’s website was hacked a month ago, but this affected articles on the blog,
This is not the first time that a Linux distro’s website has been hacked to serve malware. Indeed, there have been a small number of violations in recent months. Arch Linux’s Arch User Repository (AUR) was Targeted by Chaos Remote Access Trojan (RAT) malware in July. there was a DDos attack targeted Fedoraproject.org services in August, and a Red Hat GitLab instance was hacked A few weeks ago.
Thanks for reading..



