Remember when Microsoft presented the user account control in Windows? Designed to improve security, it gave new indications on users for some tasks. It disturbed some users that they find ways to shut down the entire UAC system on their Windows devices or be less disappointed.
A new security facility of administrator protection, Windows, May be next Security facilities that can occur on users’ veins.
Broken to its origin, the administrator asks for the Protection Authority whenever actions require administrator privileges. Think about the installation of some software, modify some Windows settings, edit the Windows Registry, or make other changes in the Windows device that require height.
Whenever such a work is started, Windows asks for security verification. You need to verify the action by entering your pin or using biometric authentication, before it is executed on the Windows machine.
The visual process makes the administrator only half of the conservation facility. When a Windows signs in the user system, they are automatically assigned a disadvantaged user token. Windows will then request the authority for the tasks that require high rights. Verification is through Windows security. Once done once, Windows produces a separate administrator tokens using a “hidden, system-generated, profile-exposed user account”, writes Microsoft on its technical community website.
Tokens are used only for that specific process and are automatically destroyed when finished. Therefore, when you initially type Regedit, you will get the Authority Prompt before the Registry Editor is opened. Once you close the window, the authority tokens are destroyed, so that the “administrator privileges no longer become” on the system.
The entire process is repeated whenever a process or function requires height.
Microsoft claims that this new security facility has many benefits on the current system:
- Windows prevents users from making accidental changes or changes by malware.
- Increases awareness to users.
- Users are always under control.
- Lack of malware.
The main advantage is that when the administrator protection is enabled, there is no auto-height now. When a task currently requires height on the Windows devices, a UAC prompt is offered a simple yes or no option to deal with it. This requires no password prompt and may always exploit malware elevated sessions or admin mode.
The new security facility can improve security, provided that Windows users do not close anything on their screen. The main negative side is that the signals can be more often, which can be annoying after a while.
However, the administrator is not capable of safety default, not at least at this level. This means that users or system administrators must enable the facility before it becomes active.
Home administrators need to weigh the advantages and disadvantages of the new system. How the Microsoft system advertises, depends on many people do not even know that it exists.
How to configure administrator safety in Windows 11
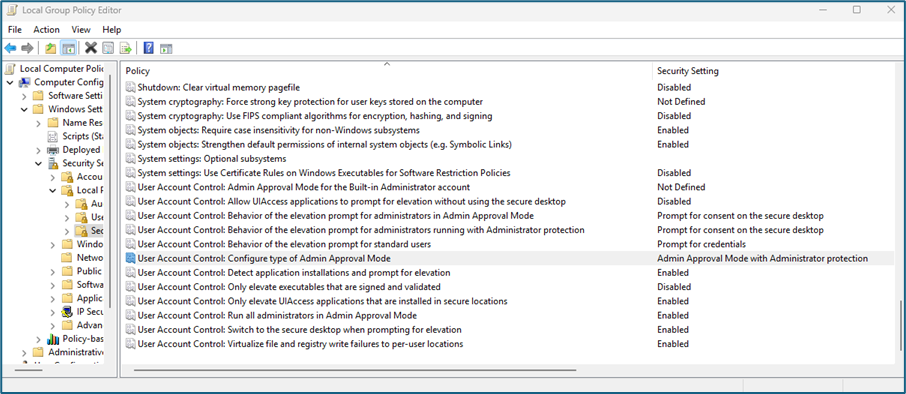
Here is described how you configure it in group policy (according to Microsoft, the settings that come at the later point). Note that this only applies to Pro, Education and Enterprise Editions of Windows 11.
- Open the start menu.
- Type gpedit.msc and press enter-key.
- Confirm the UAC Prompt.
- Computer Configuration> Windows Settings> Security Settings> Local Policies> Go to Safety Options.
- Double-click “User Account Control: Configure the type of admin mode”.
- Set it to “Admin Mode” with Administrator Protection.
- Close that policy window.
- “User Account Control: Behavior for administrators running with administrator protection to configure materials and credentials prompts”.
- The default is “signal for credentials on safe desktop”. You can turn it into a signal to consent on a safe desktop “.
- Close the group policy editor.
- Return the PC.
Microsoft has not yet disclosed when the new security facility will land into stable versions of Windows. A possible target is the upcoming feature update Windows 11, version 25h2.
Now you: What is your on administrator protection? Will you enable this feature if it lands on your Windows machine? Feel free to leave a comment below.
Thanks for reading..




